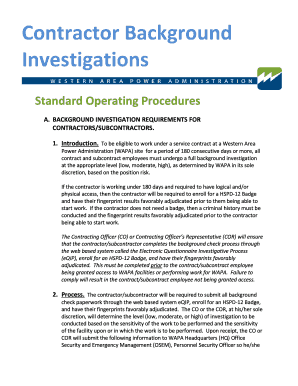
Federal contractor investigations in the USA are a critical compliance checkpoint. These inquiries, often initiated by agencies like the OFCCP, ensure contractors meet legal obligations for equal opportunity and workplace safety. Navigating them successfully is essential for maintaining government business eligibility.
Common Triggers for Federal Contractor Investigations
Imagine a federal contractor cutting corners on a crucial infrastructure project, or a whistleblower reporting suspicious billing practices. These scenarios often ignite official scrutiny. Common triggers include allegations of fraudulent billing, such as charging for unperformed work or inflating labor costs. Suspected violations of key regulations, like the Service Contract Act or Buy American Act, also prompt immediate review. Furthermore, a failure to maintain adequate cybersecurity standards to protect sensitive government data is a fast-growing catalyst. Any sign of a false claim or a compromised system can swiftly transform a routine audit into a full-scale, high-stakes investigation.
Whistleblower Complaints (False Claims Act)
For a federal contractor, the day often begins with routine operations, yet certain actions can abruptly initiate a formal inquiry. A common trigger for federal contractor investigations is a whistleblower complaint from a concerned employee alleging fraud or safety violations. Similarly, a failed audit revealing discrepancies in timekeeping or cost accounting frequently raises red flags. Even a simple mistake in mandatory reporting, like those required by the Service Contract Act, can prompt scrutiny. These events act as a catalyst, compelling agencies to examine compliance with the stringent Federal Acquisition Regulation, ensuring taxpayer funds are protected.
Cost Accounting and Pricing Discrepancies
Federal contractor investigations are often triggered by **whistleblower disclosures**, where employees report suspected fraud or safety violations. Proactive **compliance monitoring** by agencies like the DCAA or OSC can also uncover irregularities during routine audits. Other common catalysts include bid protests from competing firms, failure to meet small business subcontracting goals, and suspicious patterns in timekeeping or cost reporting. Staying vigilant against these **common triggers for federal contractor investigations** is essential for maintaining contract integrity and avoiding severe penalties.
Failure to Meet Small Business Subcontracting Plans
Federal contractor investigations often start from specific red flags. Common triggers include a **whistleblower complaint** from a current or former employee, which is a powerful catalyst. Suspected violations of the False Claims Act, like overbilling for labor or materials, are a major focus. Other frequent issues are failures in mandatory cybersecurity compliance, allegations of employment discrimination, or suspected conflicts of interest.
A single hotline tip can quickly escalate into a full-scale audit.
Staying proactive with internal controls and training is the best defense for government contractors navigating these complex rules.
Non-Compliance with Socioeconomic Programs (e.g., 8(a), SDVOSB)
Federal contractor investigations often start from specific red flags. A major compliance violation trigger is a whistleblower tip, where an employee reports suspected fraud internally or to a government hotline. Other common catalysts include routine audits uncovering billing discrepancies, failures to meet small business subcontracting plans, or mandatory disclosure lapses where a contractor didn’t report credible evidence of wrongdoing. Even a competitor’s protest over a lost bid can spark a deep review into your company’s past performance and compliance records.
Security Violations and Safeguarding Classified Information
Federal contractor investigations are commonly triggered by whistleblower disclosures alleging fraud, waste, or abuse. Proactive data analytics by oversight agencies frequently flag irregularities in billing or labor charges. A company’s failure to meet small business subcontracting plans or prevailing wage requirements under the Davis-Bacon Act also prompts scrutiny. Furthermore, a lack of adequate compliance systems is a primary red flag for auditors. These triggers ensure accountability in government contracting and protect taxpayer funds from misuse.
Labor Law Violations (Davis-Bacon Act, Service Contract Act)
Federal contractor investigations are frequently triggered by **whistleblower disclosures**, which are protected reports of suspected fraud or abuse. Other common catalysts include routine audits by agencies like the DCAA, findings of non-compliance during pre-award surveys, and tips from competitors. Failure to meet small business subcontracting plans or violations of the Service Contract Act and Davis-Bacon Act also prompt scrutiny. Proactive **compliance with federal acquisition regulations** is the most effective defense against these disruptive and costly inquiries.
Key Investigating Agencies and Their Roles
Key investigating agencies form the backbone of a nation’s security and justice framework, operating with specialized mandates to combat complex threats. The federal bureau of investigation tackles domestic terrorism and cybercrime, while the Central Bureau of Investigation in India handles major inter-state cases. Agencies like the National Investigation Agency focus on terror-related offenses, and the Enforcement Directorate pursues financial crimes. These entities, through rigorous intelligence gathering and forensic analysis, ensure national integrity and uphold the rule of law, making them essential pillars of public safety and democratic governance.

The Department of Justice (DOJ) and U.S. Attorneys’ Offices
In the intricate tapestry of national security, key investigating agencies act as specialized weavers, each threading unique expertise to uphold the law. The Federal Bureau of Investigation (FBI) safeguards the United States from terrorism and cybercrime, while the Central Bureau of Investigation (CBI) in India tackles complex corruption cases. Across the Atlantic, the UK’s National Crime Agency (NCA) leads the fight against organized crime. These premier law enforcement agencies operate with distinct mandates, yet their collective mission is universal: to investigate serious offenses, gather intelligence, and bring perpetrators to justice.
Their work often unfolds in the shadows, a silent, relentless pursuit that forms the bedrock of public safety and institutional integrity.
The Defense Contract Audit Agency (DCAA)
Key investigating agencies are specialized government bodies tasked with enforcing specific laws and maintaining national security. The Federal Bureau of Investigation (FBI) is the primary federal law enforcement and domestic intelligence agency in the United States, handling crimes like terrorism and cybercrime. The Central Bureau of Investigation (CBI) in India investigates major interstate cases and corruption. In the UK, the National Crime Agency (NCA) tackles organized and serious crime. These agencies are crucial for **national security investigations**, operating with distinct jurisdictional mandates to uphold the rule of law.
The Defense Counterintelligence and Security Agency (DCSA)
Key investigating agencies form the critical backbone of national security and law enforcement. The Federal Bureau of Investigation (FBI) combats domestic terrorism and cybercrime, while the Central Intelligence Agency (CIA) gathers foreign intelligence. Specialized bodies like the Drug Enforcement Administration (DEA) target narcotics networks, and the National Security Agency (NSA) handles signals intelligence. These premier law enforcement organizations operate with distinct mandates to protect citizens and uphold justice, ensuring a multi-layered defense against complex threats both at home and abroad.
The Agency Office of Inspector General (OIG)
Key investigating agencies are specialized government bodies that uphold national security and law. In the United States, the Federal Bureau of Investigation (FBI) handles domestic threats and federal crimes, while the Central Intelligence Agency (CIA) focuses on foreign intelligence. These organizations often collaborate on complex transnational cases. Similarly, the National Investigation Agency (NIA) in India tackles terrorism nationwide. The role of these agencies is critical for maintaining public safety and ensuring national security through rigorous investigations. Their work forms a cornerstone of modern law enforcement and intelligence gathering.
The Small Business Administration (SBA) Office of Inspector General
Key investigating agencies are specialized government bodies that enforce laws and maintain national security. In the United States, the Federal Bureau of Investigation (FBI) handles domestic terrorism and federal crimes, while the Central Intelligence Agency (CIA) focuses on foreign intelligence and counterintelligence. These organizations often collaborate on cases with both domestic and international dimensions. Their critical work in law enforcement is essential for upholding justice and protecting citizens from complex threats. Understanding the role of federal law enforcement is key to appreciating national security structures.
The Investigation Process: Stages and Procedures
The investigation process is a meticulous sequence of stages designed to uncover facts and establish truth. It typically begins with the initial case intake and a preliminary assessment to determine scope. This leads into the detailed evidence collection phase, where interviews, documentation, and forensic analysis occur. Findings are then rigorously analyzed and corroborated before culminating in a comprehensive report. Adherence to this structured procedure ensures investigative integrity, provides a defensible audit trail, and is fundamental for achieving actionable and reliable outcomes upon which sound decisions can be made.
Initial Audit or Inquiry
The investigation process is a structured methodology for uncovering facts and resolving incidents. It typically begins with the initial alert and a critical **preliminary assessment** to determine scope. Investigators then systematically **collect and preserve evidence**, ensuring a documented chain of custody. This is followed by a rigorous **analysis phase** where data is examined for patterns and causality. The process culminates in **reporting findings** and, if applicable, recommending corrective actions to prevent recurrence. This systematic approach is essential for **effective incident response management** and organizational learning.
Formal Investigation and Evidence Gathering
The investigation process is a structured journey from initial alert to final resolution, demanding meticulous attention to detail at every stage. It begins with the crucial incident response and evidence collection phase, where securing the scene and preserving digital or physical artifacts is paramount. Investigators then move to analysis, piecing together timelines and motives through forensic examination and interviews. This careful reconstruction often reveals the hidden narrative behind the facts. The process culminates in reporting findings and, where applicable, presenting evidence for legal proceedings, ensuring accountability and closure.
Interviews and Employee Testimony
The investigation process is a structured method for uncovering facts. It typically begins with the initial allegation and a crucial step: securing the scene to preserve evidence. Following this, investigators collect physical and digital evidence, interview witnesses, and analyze all the gathered information to form a timeline. This **systematic investigative approach** ensures no critical detail is overlooked. A final report details the findings, which may lead to corrective action or legal proceedings.
Ultimately, the core of any successful investigation is the meticulous documentation of every step, creating a clear and defensible audit trail.

The Decision to Prosecute or Pursue Administrative Remedies
The investigation process is a systematic sequence designed to uncover facts and establish truth. It typically begins with the initial case intake and assessment, where scope and jurisdiction are determined. This is followed by the critical evidence collection and preservation phase, ensuring chain of custody. Investigators then proceed to analysis, interviews, and finally, reporting and case closure. A methodical approach is paramount for investigative integrity and legal defensibility, forming the backbone of any professional inquiry. Adhering to structured investigation protocols is essential for reliable outcomes and maintaining procedural fairness.
Settlement Negotiations and Agreements

The investigation process is a systematic sequence of stages designed to uncover facts and establish truth. It typically begins with the initial allegation and a crucial **preliminary assessment** to determine scope. This leads to the formal **planning and scoping phase**, a critical step for effective case management. Investigators then proceed to the **evidence collection stage**, gathering documents, conducting interviews, and securing digital data. All findings are meticulously analyzed before a final report is compiled, presenting conclusions and recommendations. This structured approach ensures investigative integrity and reliable outcomes for all stakeholders.
Potential Consequences and Outcomes
Potential consequences and outcomes represent the possible results of an action or decision, ranging from beneficial to detrimental. A thorough analysis of these possibilities is a critical risk management tool, allowing organizations and individuals to prepare for various scenarios.
Failing to anticipate negative outcomes can lead to severe operational, financial, or reputational damage, even from well-intentioned initiatives.
Conversely, understanding positive potential can drive innovation and strategic advantage. Ultimately, a balanced assessment of consequences informs better planning and more resilient decision-making, turning uncertainty into a manageable variable.
Civil and Criminal Penalties
Understanding potential consequences and outcomes is essential for strategic risk management. Proactively analyzing these factors allows organizations to mitigate threats and capitalize on opportunities, directly influencing long-term viability. A failure to assess downstream effects can lead to operational failures, financial loss, and reputational damage. Conversely, a thorough evaluation enables informed decision-making and builds stakeholder confidence. This foresight is a critical component of sustainable business growth, ensuring resilience in a dynamic market.
Suspension and Debarment from Federal Contracting
Potential consequences and outcomes form the critical nexus of every decision, shaping future realities. Anticipating these results allows for strategic planning and risk mitigation, turning uncertainty into a navigable path. A proactive assessment of potential outcomes is a cornerstone of **effective risk management strategies**, empowering organizations to seize opportunities while safeguarding against pitfalls. This forward-looking approach transforms challenges into catalysts for innovation and sustainable growth, ensuring resilience in a dynamic world.
Contract Termination and Financial Restitution
Understanding potential consequences and outcomes is fundamental to effective risk management strategy. Proactively mapping possible scenarios allows organizations to allocate resources wisely, mitigate negative impacts, and capitalize on positive opportunities. A failure to conduct this analysis often leads to reactive decision-making, financial loss, and reputational damage. Ultimately, the goal is not to predict the future with certainty, but to be prepared for its many possibilities. This disciplined approach builds organizational resilience and provides a clear competitive advantage in volatile markets.

Mandatory Compliance Program Implementation
The path of innovation is paved with both promise and peril. A single technological breakthrough can spark a global economic transformation, creating new industries while rendering others obsolete. This cascade of change reshapes job markets, redefines social interactions, and challenges our ethical frameworks. The ultimate outcome hinges on our foresight; proactive governance can harness potential for widespread prosperity, whereas unchecked advancement risks deepening inequality and creating unforeseen vulnerabilities for society.
Corporate Integrity Agreements (CIAs)
The potential consequences of inaction are severe, ranging from operational paralysis to catastrophic financial loss. Proactive risk management, however, unlocks positive outcomes like sustained growth and market leadership. Navigating this landscape effectively is essential for long-term business resilience, ensuring an organization can withstand shocks and capitalize on opportunities. A robust strategy directly influences competitive advantage, turning potential threats into a durable foundation for success.
Best Practices for Prevention and Response
Strong prevention starts with proactive habits. Regularly update software to patch security holes, use strong and unique passwords, and educate your team on spotting phishing attempts. For response, having a clear, tested incident plan is key. This should define roles for crisis communication and immediate steps to isolate affected systems. Remember, the goal is to contain the issue quickly, recover operations, and learn from the event to improve your security posture for next time.
Q: What’s the first thing to do during a security breach?
A: Immediately isolate the affected system or network segment to prevent the threat from spreading, then activate your incident response team.
Establishing a Robust Internal Compliance Program
Effective risk management weaves prevention and response into a single, resilient strategy. Proactive measures, like regular employee training and robust access controls, form the first critical line of defense. *Yet, even the best plans must anticipate a breach.* A swift and practiced incident response is paramount for business continuity, minimizing downtime and preserving customer trust. This integrated approach ensures an organization is not merely reactive but resilient, turning potential crises into managed events. Adopting a **cybersecurity framework** provides the essential structure for this continuous cycle of improvement and adaptation.
Conducting Regular Internal Audits and Training
Effective prevention and response strategies form the cornerstone of organizational resilience. A proactive security posture begins with comprehensive risk assessments and continuous employee training to identify and mitigate threats before they materialize. This foundational work is crucial for building a robust incident response plan, ensuring teams can act employee reviews on Glassdoor swiftly and decisively. When an incident occurs, a clear, practiced containment and communication protocol minimizes damage and accelerates recovery, turning potential crises into managed events. This cycle of preparation and action is essential for maintaining operational continuity and stakeholder trust in a dynamic threat landscape.
Implementing a Clear Whistleblower Policy
Effective prevention and response strategies form the cornerstone of organizational resilience. A proactive approach involves conducting regular risk assessments and implementing robust security protocols to mitigate threats before they materialize. This foundational work is critical for maintaining operational continuity.
A thoroughly tested and communicated incident response plan is the single most important factor in minimizing damage during a crisis.
Following an event, a clear focus on containment, eradication, and recovery, followed by a detailed post-incident review, closes the loop. This cycle of continuous improvement strengthens overall security posture and ensures the organization is better prepared for future challenges, a key principle for effective risk management.
Securing Legal Counsel at the First Sign of an Investigation
Imagine a workplace where safety is woven into daily habits. The cornerstone of effective risk management is a proactive culture of prevention. This begins with thorough training and clear protocols, turning awareness into instinct. When an incident occurs, a swift and practiced response is critical. Having a dedicated incident response team ready to execute a pre-defined plan minimizes damage and accelerates recovery. Ultimately, integrating these best practices into organizational DNA not only protects assets but also builds resilient operations that can withstand and learn from challenges.
Cooperating with Investigators While Protecting Rights
Effective prevention and response strategies form the cornerstone of organizational security. A proactive approach begins with comprehensive risk assessments and continuous employee training to foster a culture of awareness. This foundation of **cybersecurity awareness training** is critical. For response, a clear, tested incident response plan ensures swift action to contain breaches and recover operations, minimizing damage and maintaining stakeholder trust.